DynamoDB Streams
AWS’s DynamoDB is a managed NoSQL data store (non-relational data store). Often, we will want some sort of audit or logging of who is changing data. This can be done using DynamoDB streams. DynamoDB Stream will send all changes to a Lambda function we write.
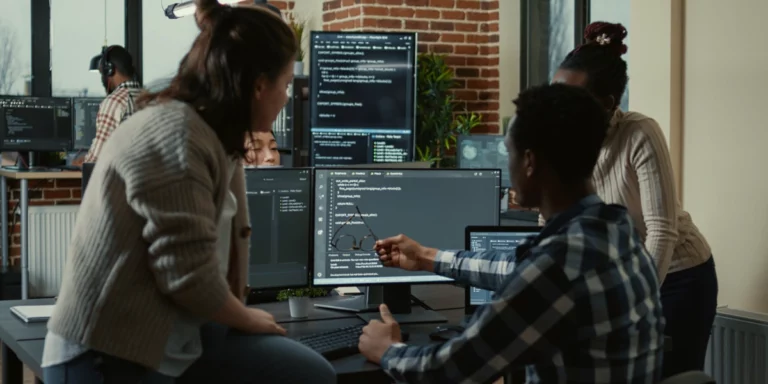
First, let’s create a new Lambda function.
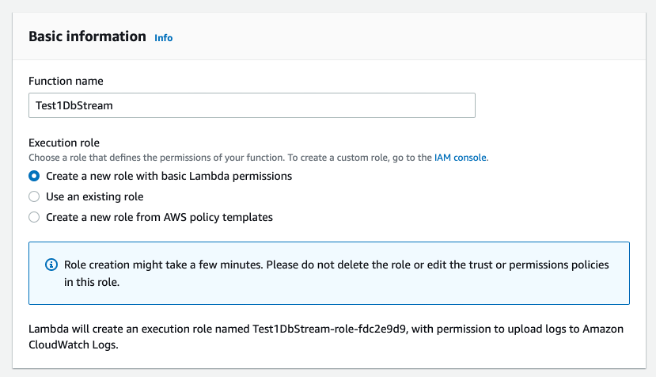
The code just logs the request to CloudWatch.
Create DynamoDB Table and configure it as you need.
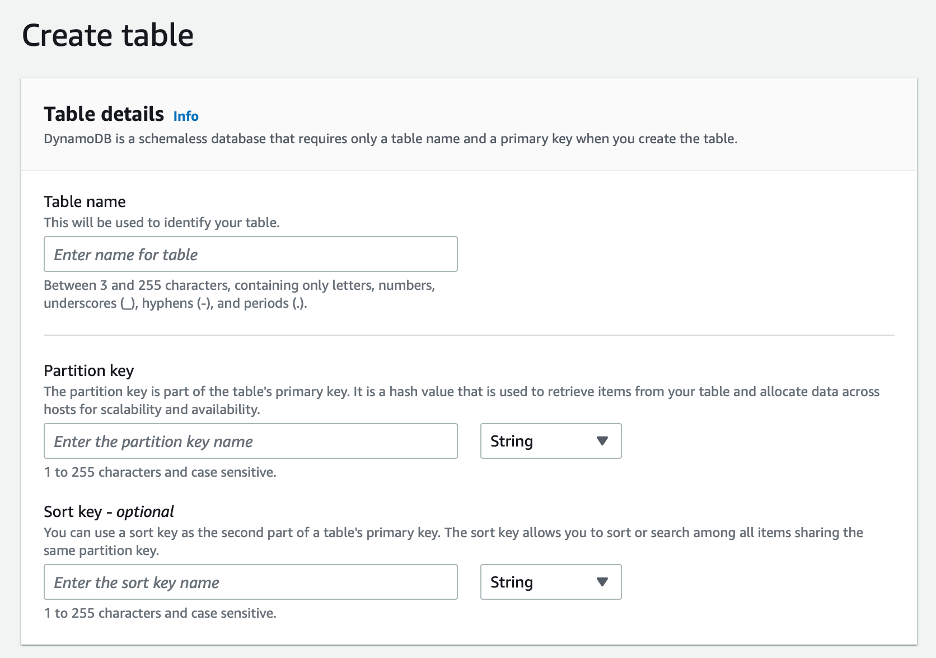
After you create the DynamoDB table, it is time to create a DynamoDB Stream. Go to the Exports and streams tab on your DynamoDB table.
From the Exports and streams tab, we can enable DynamoDB Stream for this table.
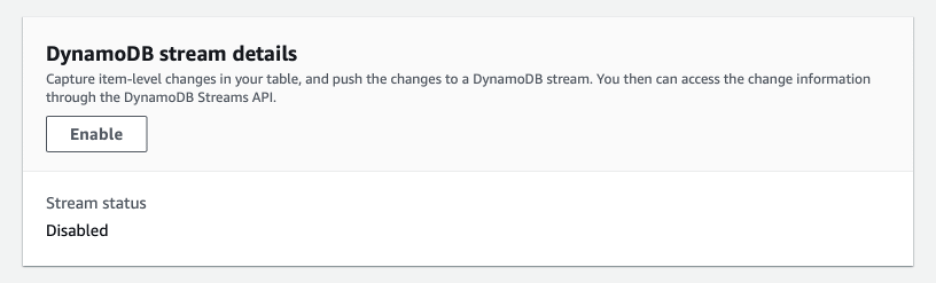
You can configure the stream to contain different information. The Key attributes only type is the default. Sending only the key attributes won’t allow us to analyze the data that has changed. For that level of detail, you will need to select one of the other options. If you need to change this option, you will have to first disable the stream and then enable it again.
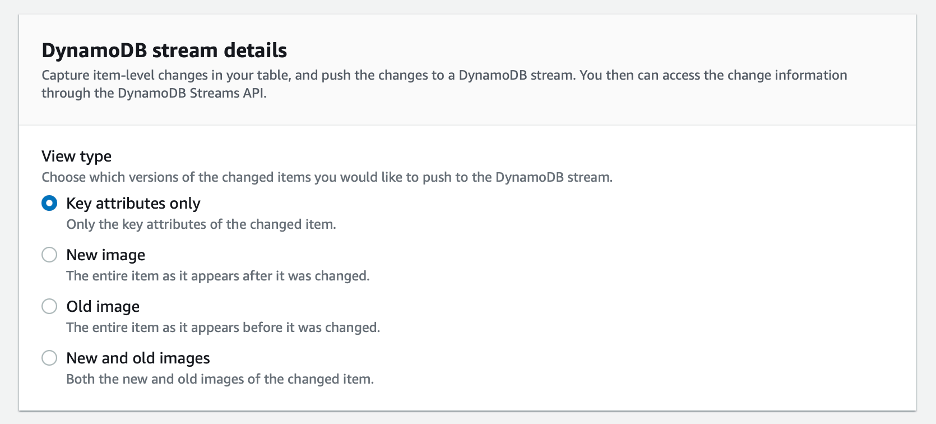
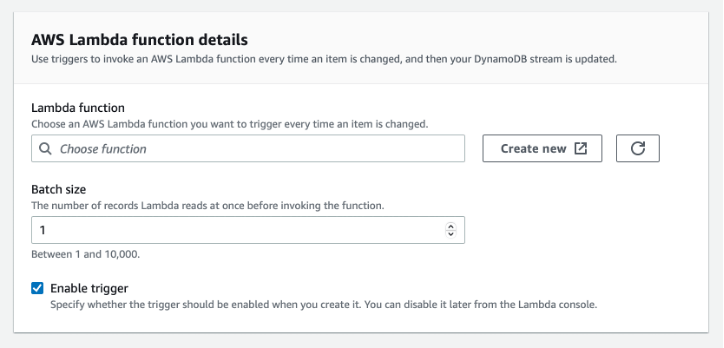
Once you have created your stream, you need to create a trigger. The trigger will call your Lambda function when data is changed.
While trying to create your Lambda function, you might end up with a permission problem. Actually, I bet you do. You will get an error like the one below.
InvalidParameterValueException: Cannot access stream arn:aws:
dynamodb:us-east-1:abc:table/Test1/stream/2022-09-29T14:41:31.573.
Please ensure the role can perform the GetRecords, GetShardIterator,
DescribeStream, and ListStreams Actions on your stream in IAM.
We will need to create a policy and associate it with our Lambda function.
Go to Policies within IAM (Identity and Access Management) in the AWS Console.
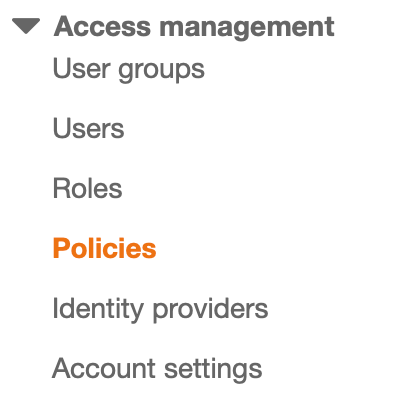
Then click Create policy.
![]()
When creating a policy, you can use the visual editor or JSON. In this case, we will be using the JSON version. Click the JSON tab and insert the JSON for the policy.

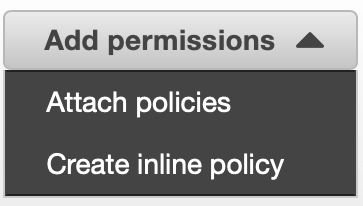
Attach the policy to the role for your Lambda function. Find the role for your Lambda, and then attach the policy to it.
![]()
Now go back and create the trigger and associate it with your Lambda function.
![]()
As you make changes to your data in your DynamoDB table, you should receive logs written to CloudWatch for each change.
Results based on this setup might look like the below.
While not super trivial to set up, DynamoDB Streams gives us a powerful way to track what is changing in our DynamoDB table.
References
https://docs.aws.amazon.com/amazondynamodb/latest/developerguide/iam-policy-read-stream-only.html